TLS Options
A TLS network interface requires TLS options to collect syslog messages.
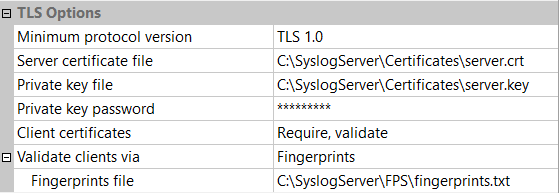
Server Key and Certificate
The server certificate file is in PEM format. A certificate chain must be sorted starting with the actual server certificate, then intermediate CA certificates if applicable, and ending at the highest level (root) CA.
The server private key is in PEM format in Base64 ASCII encoding. Do not forget to specify the password if the key file is encrypted.
If the private key and the server certificate are in the same file, set its path twice in both fields.
Client Certificate Validation
Syslog Watcher can optionally validate client certificates to collect syslog messages from only authorized entities.
Certificate Fingerprints
A certificate fingerprints file is a text file associating client IP addresses and fingerprints of client certificates. It contains one pair per line: an IP address and a certificate fingerprint. Here is an example with two clients:
192.0.2.1 sha1:56:97:8E:2C:39:74:62:DB:78:5F:E6:CB:3B:D2:B9:02:C0:81:1F:E6
2001:0db8:85a3:0000:0000:8a2e:0370:7334 sha1:4B:9A:53:B1:E6:0E:FE:E9:BA:6D:BE:96:B3:18:F9:07:06:D7:89:D2
How it works
Syslog Watcher:
-
Obtains a client certificate;
-
Calculate the certificate fingerprint;
-
Checks if the fingerprint file contains this fingerprint associated with the sender's IP address;
-
Refuse any connection that has no match in the fingerprint file.
After a connection attempt, Syslog Watcher dumps the refused certificate fingerprint in its own log. To allow that client, copy the fingerprint from there and add it to the fingerprint file.
Certificate Authority (CA) File
A certificate authority (CA) file contains one or more CA certificates for verification purposes. CA certificates are in PEM format and identified by the following sequences:
-----BEGIN CERTIFICATE-----
... (CA certificate in base64 encoding) ...
-----END CERTIFICATE-----
Certificate Authority (CA) Folder
A certificate authority (CA) folder contains CA certificates in PEM format. Each file contains one CA certificate. The files are looked up by the CA subject name hash value. CA certificates with the same name hash value differ in extension, e.g. 9da13359.0, 9da13359.1 etc.